
Cybersecurity is a rapidly evolving field, and landing a job in this domain requires more than just technical skills - it demands a strong understanding of security principles, real-world threats, and problem-solving abilities. No matter if you're preparing for an entry-level role or a senior position, cybersecurity interviews often test your knowledge in various key areas such as encryption, network security, ethical hacking, risk management, and more.
To help you prepare effectively, I have created a list of most asked cybersecurity interview questions with detailed answers to the professionals of all levels. Topics include fundamental concepts, scenario-based problem-solving, and best practices. This guide will give you insight into what hiring managers expect and how to confidently answer their questions.
Let's start.
Nowadays, Cybersecurity is a critical technology for organizations to secure their sensitive data and other assets. This service helps them to safeguard their personal information and business strategies. Due to this huge demand, major companies are recruiting experts, which makes it one of the most prominent career paths.
To get these job opportunities and become a part of these organizations, one must clear the interview. The interviewer asks different kinds of questions based on the job descriptions. The questioner evaluates candidates' capabilities from fundamental principles to advanced topics. Given are some most asked interview question and their answers too.
Explore igmGuru's Cybersecurity course to advance your career for a better growth.
The first step is to begin with some basic cybersecurity interview questions for freshers.
Cryptography in cybersecurity refers to the process wherein information is coded or hidden. This ensures that only the person for whom the message was for can decode/ read it.
Traceroute is basically an impactful network diagnostic tool. It enables users to track down the path taken by data packets, right from the source to the destination over the internet.

The CIA triad stands for confidentiality, integrity & availability. This security model is used by organizations to ensure IT security.
In cyber security, a firewall is basically a wall that tracks all outgoing and incoming traffic to block hackers from performing any malicious activity. It helps in maintaining data privacy from phishing links, trojan viruses, worm viruses, etc.
A honeypot refers to a network-attached system that is implemented as a decoy to attract cyberattacks. This helps the cybersecurity team in detecting the attackers, deflecting them and studying the hacking attempts.
Related Article- Cyber Security Tutorial
These cyber security job interview questions are crafted for intermediates interested in securing a higher-level job in this field.
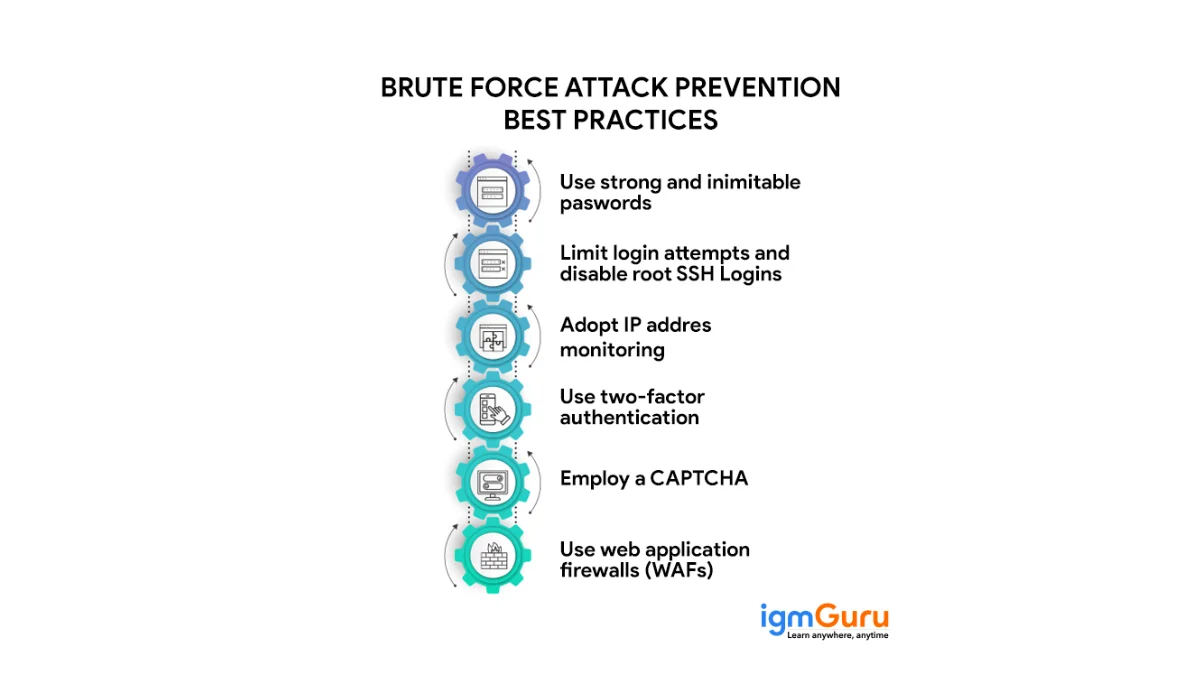
Brute force attack in cyber security is a hacking method. It employs trial and error to crack encryption keys, login credentials and passwords. This simple yet effective tactic helps many attackers gain unauthorized access to organization's networks and systems and individual's accounts.
Brute force reflects the brutal ways and force used to get into the user accounts.
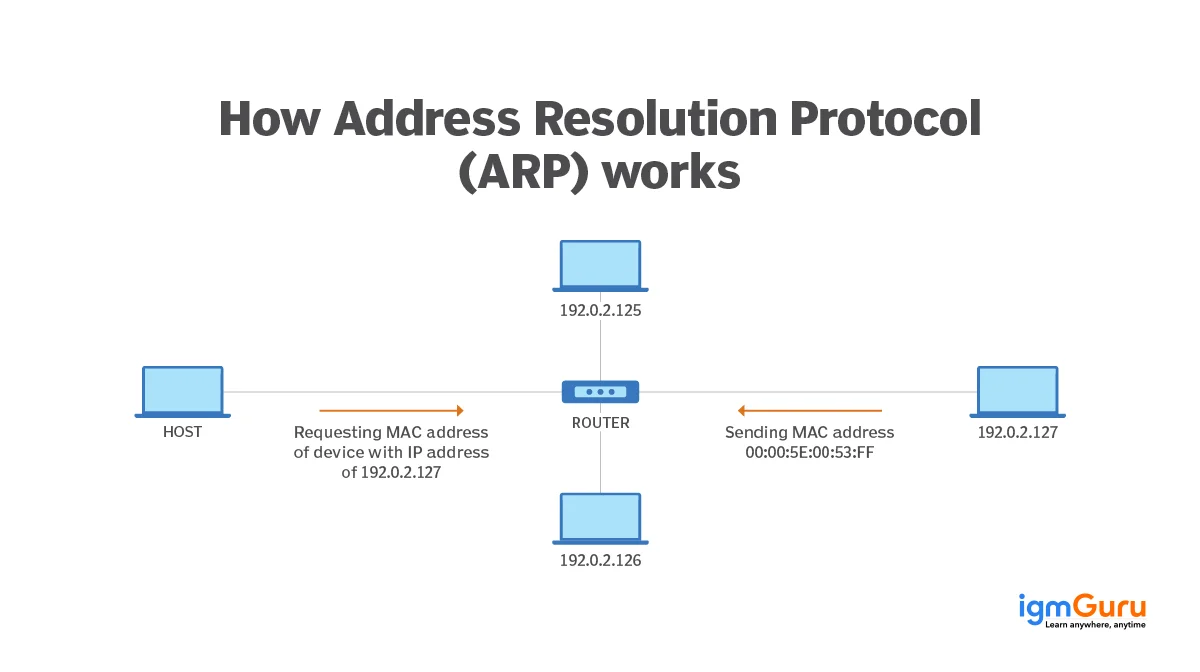
Address Resolution Protocol (ARP) is the network layer's communication protocol in the OSI (open systems interconnection) model. It paves a bridge between a fixed physical machine address (MAC) and a constantly-changing internet protocol (IP) in a LAN.
It works between Layer 2 and 3 of the OSI model, wherein the MAC address exists on Layer 2, while the IP address is on Layer 3.
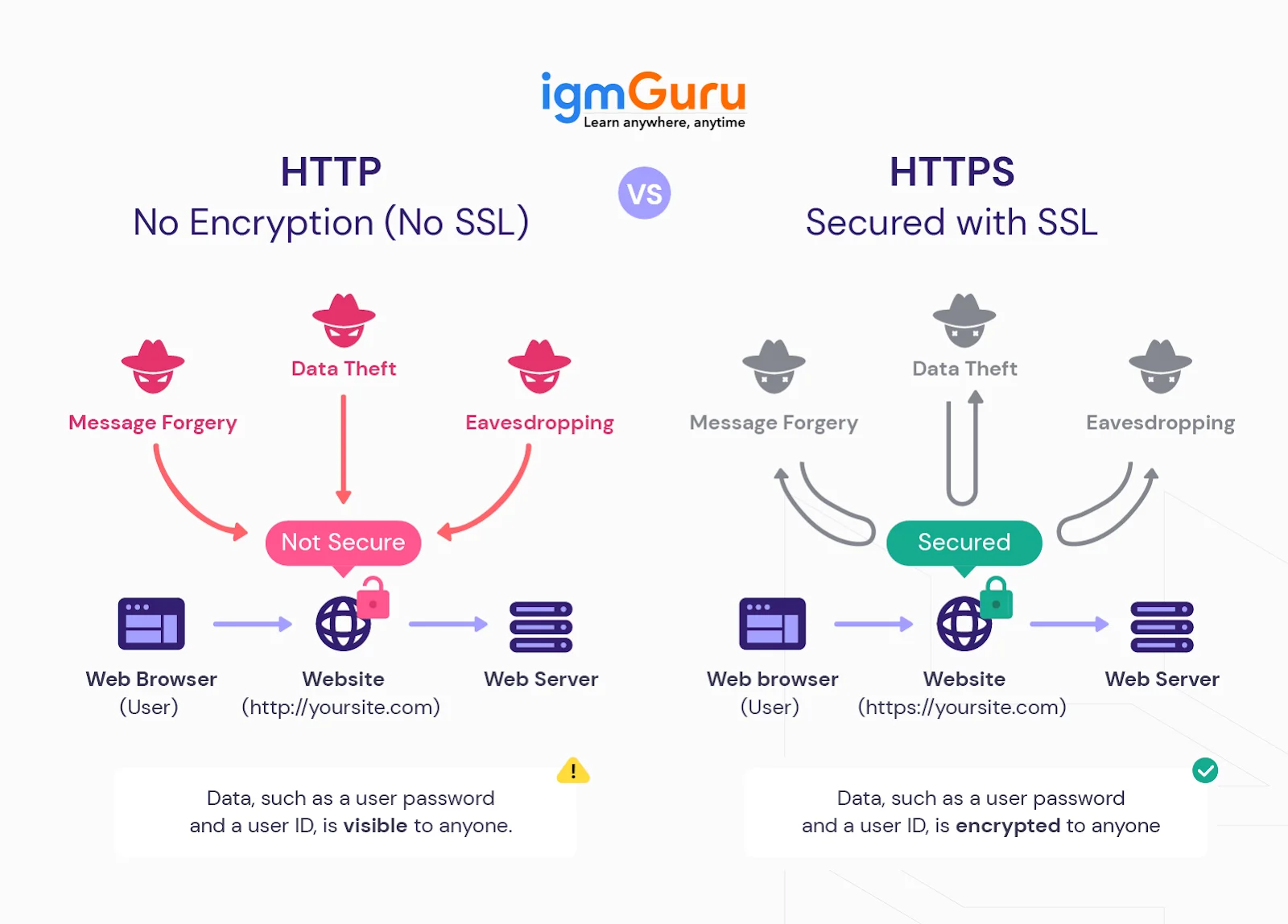
SSL stands for Secure Sockets Layer, which is a technology that enables two (or more) systems/parties to securely communicate over the internet. It works in addition to HTTP at the presentation layer.
HTTPS, on the other hand, stands for Hypertext Transfer Protocol Secure. It combines SSL and HTTP, along with encryption to provide a hyper secure surfing experience. Its working includes the four upper layers of the OSI model.
Sniffing tools are basically a special type of software or hardware that can intercept the data packets traveling through the Internet. They capture these data packages to analyze them, allowing users to ensure if there is threats or malicious information in them. Ultimately, they capture, log and analyze network traffic to reveal details like source and destination addresses, content and even sensitive information. Here are some of the common sniffing tolls we use in cyber security -
DDoS is a type of cyber crime where the hacktivists provide a huge amount of traffic on any site to restrict the users to access it. It is very common these days. The reasons vary depending on the intention of hackers.
Some individuals do it for fun or make a point and some competitors do it for growth hacking. These types of attacks can cause a significant loss for businesses.
Related Article - How To Learn Cybersecurity?
At an advanced level, you must go through these common cyber security interview questions and answers for experienced professionals.
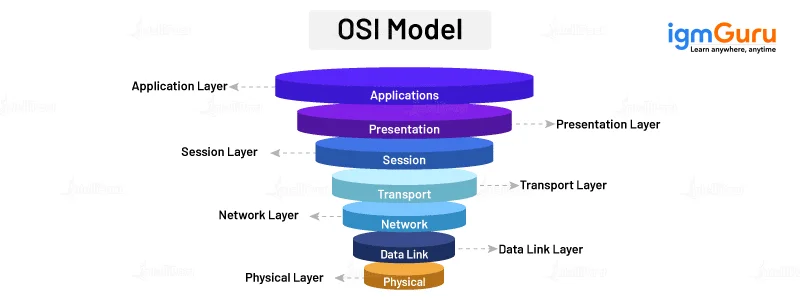
Here is a list of the OSI model layers
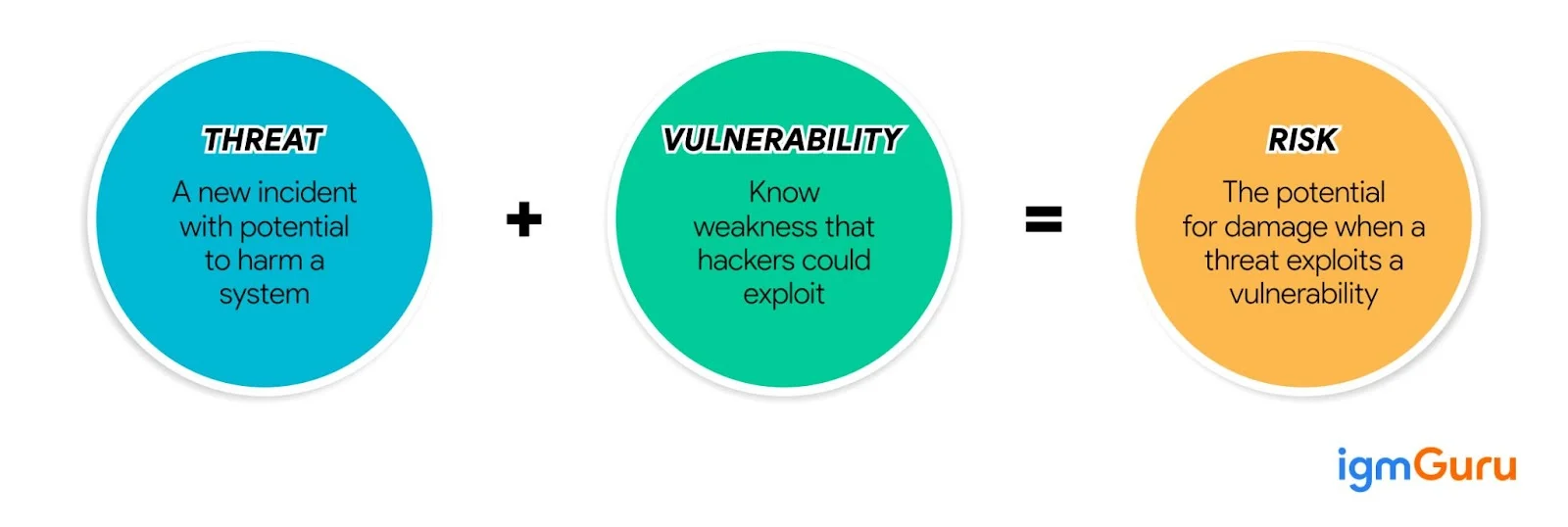
Risk management is a crucial process in the cyber security field. It entails identifying potential threats, analyzing their impact and constructing the best plan of action. This never-ending process is possible by understanding risk, which itself is the product of threat and vulnerability.
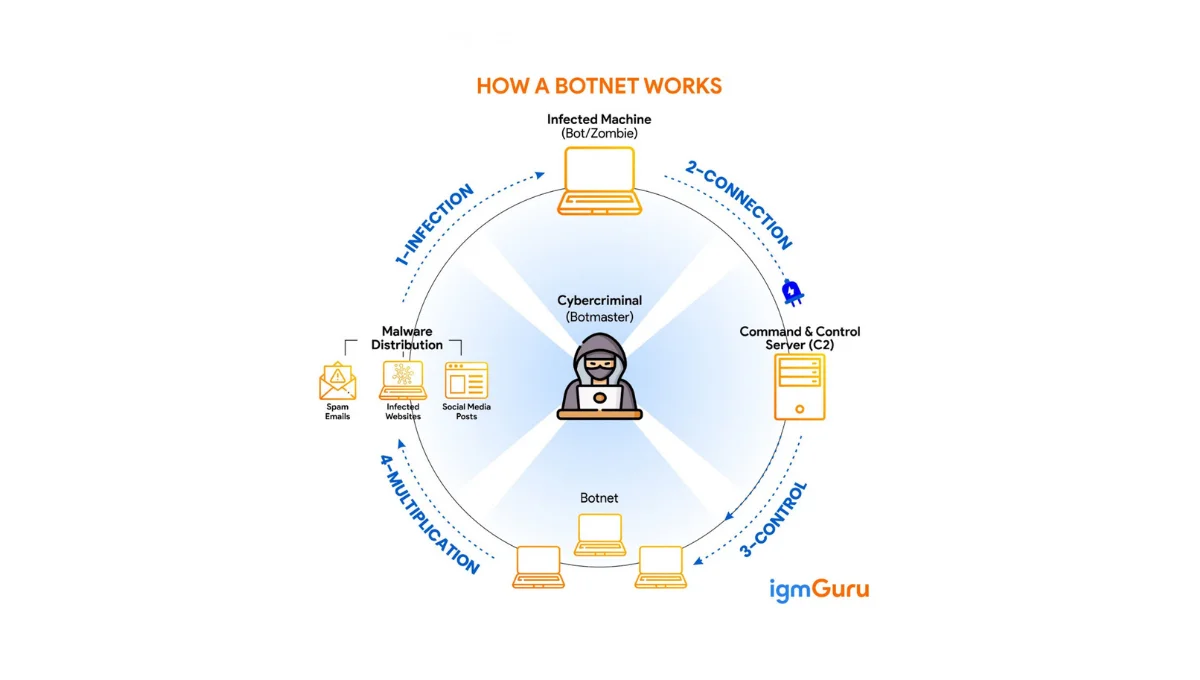
A botnet is an accumulation of internet-connected devices that get infected with malware and can even be controlled by it. These can be mobile phones, servers and PCs. It is extensively used for stealing data, launching distributed denial-of-service attacks (DDoS), sending spam and much more.
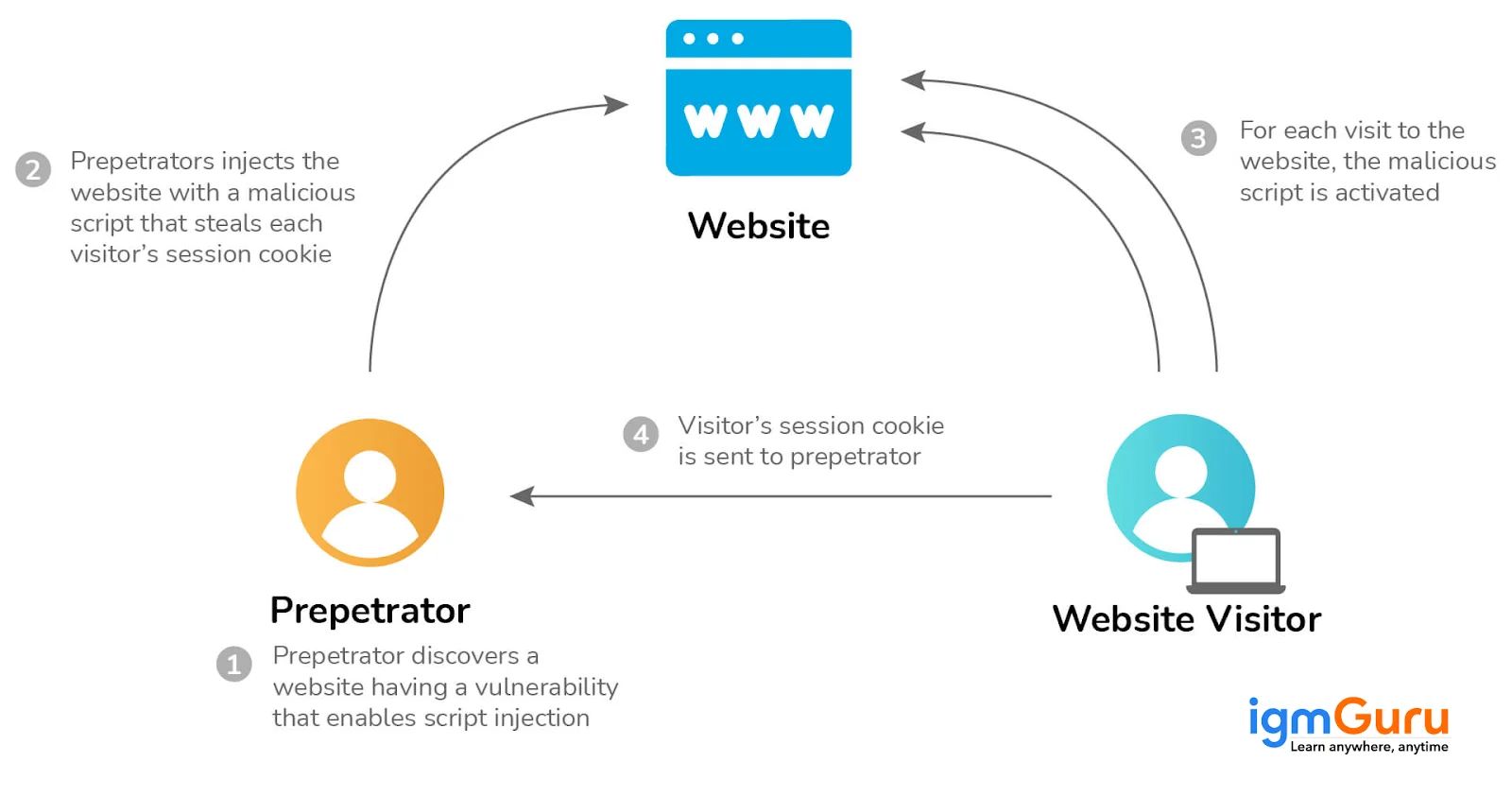
XSS is the short form of cross-site scripting, which is a web security flaw that leaves a gap for an attacker to manipulate and determine how users interact with the susceptible app.
Preventing is both simple and easy, swayed by the app's sophistication and user-controllable data handling. These are some ways to prevent it
DoS and DDoS attacks differ from one another in the following ways.
| Parameter | DoS Attack | DDoS Attack |
| Source of Attack | It usually originates from a limited or single source that is under the attacker's control. | It employs a distributed network of compromised devices. This renders it more difficult to mitigate and identify the attack. |
| Attack Method | The target network or system is flooded by a small group of sources or even a single source. High volume of requests or traffic is sent to overwhelm the resource. | Botnet is formed by compromised devices or computers via multiple sources. The target is bombarded collectively. |
| Detection & Mitigation | It is comparatively easier to detect and mitigate this attack because the source is single/limited. | Since the source is varied, detecting and mitigating the attack becomes a challenge. |
Explore these top trending Cybersecurity certifications.
These cyber security analyst interview questions or Cybersecurity interview questions will help you get the job of your dreams.
Patch management must be implemented as soon as any software updates are released. It is imperative for all network devices present within an enterprise to undergo in less than a month.
DDoS is the acronym of distributed denial-of-service, which is an attack that overwhelms the target network, system or site with excessive traffic flow. This renders the target inaccessible to its target users.
It happens mainly in two ways

Data leakage describes unauthorized release of information or data to a third party from the business' end. It can happen through storage devices, email, internet or mobile data. Three types of data leakage are
Typically these steps are followed during a CSRF attack
VPN is a technology that helps to create a secure and encrypted connection over a public network. This encryption protects the data and secures the IP address to provide online privacy and security. VPNs are commonly used to protect sensitive data, bypass geographic restrictions and avoid censorship.
Also Read - Top Network Security Certifications For Beginners
This section of the blog consists of the most often-asked cyber security engineer interview questions or Cybersecurity interview questions. So, if this is the job title that aligns with your expertise, then follow through.
Encryption is the method that ensures data is rendered unreadable by everyone apart from those who have the secret key needed to decrypt the data. It is employed to ensure security of data over private connections.
Encoding is a method employed to ensure that the data is correctly formatted to be interpreted rightly by recipients and apps. Communication is made possible by transforming into an easy-to-read scheme.
Hashing methodology is used to help maintain data's integrity. A data hash refers to a string of data generated against the preserved information. This helps in comparing the original and transmitted data.
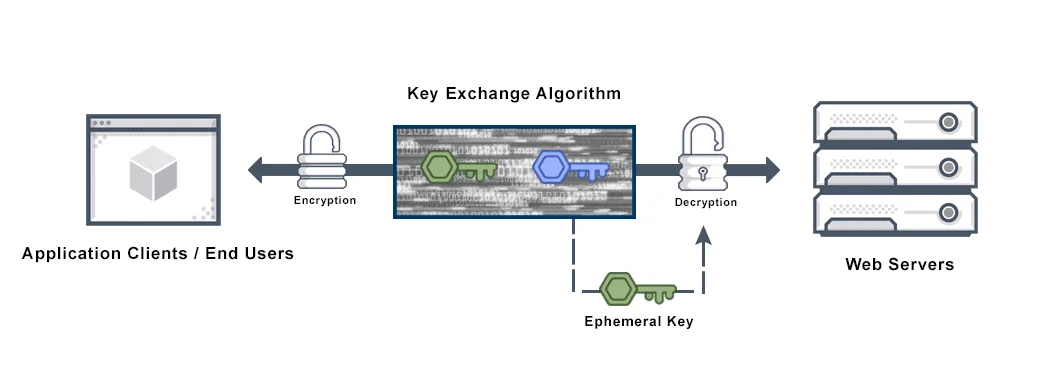
Perfect forward secrecy (PFS) is an encryption system that automatically and frequently alters the keys involved in encryption and decryption of information. It is an ongoing process that ensures minimal exposure of data in case of hacking.
WEP crack is a type of attack that exploits the vulnerabilities of the WEP (wireless equivalent privacy) protocol. This protocol was an early encryption method for securing wireless networks.
Network sniffing is basically a technique employed to evaluate the data packets that are delivered throughout the network. Specialized hardware and software is utilized to accomplish this task. Sniffing is employed for various purposes such as
The system hardening is a process of minimizing cyber threats risks by compressing the attack surface. This involves using a set of tools to manage vulnerability of organizational systems, firmware, applications, etc. some common types of system harding are -
Related Article- Role of Artificial Intelligence (AI) in Cyber Security
Network security interview questions are integral to help you get started and find your successful spot in this field.
The software development method used to write and test various versions of a software program simultaneously is called pipelining. It is quite similar to parallel processing, except that it works more in depth. As many programs run parallel to one another, weeks or months worth of work gets done in a few hours.
MAN or metropolitan area networks are engaged to connect multiple computers in different cities. With its large geographic scope, it may work as an internet service provider (ISP). These are less reliable, congested and difficult to establish and maintain.
Wi-Fi security means protecting networks and devices connected in a wireless environment. If there is no Wi-Fi security, then networking devices such as a router or a wireless access point can be easily accessed by anyone. This can be done with a mobile device or computer that is within the router's wireless signal range.
Stateful inspection in networking is a firewall technology. Also called dynamic packet filtering, it is used to monitor the condition of active connections, using this data to judge which network packets should be allowed through the firewall.
Null session is a type of cyber attack that is of concern in Windows 2000, Windows XP and Windows Server 2003. The system administrators do not consider it while creating network security measures for modern Windows versions. However, it is still a point of concern for individuals using older versions.
Attackers can plan this attack to steal important information from their system to get remote access. Once they successfully perform this attack, they can access the system from anywhere including confidential data.
Related Article- Top Cybersecurity Trends To Follow
For those who already have experience in the field, these cybersecurity scenario-based questions and answers will be extremely useful.
The attachment must not be downloaded. It could have malware, bugs or viruses, which may lead to corruption in the system. The link could also take on an unauthenticated third page, comprising safety. Also, it is quite easy to make a fake email id, which could also be the case here.
Dear XYZ, Due to inactivity, your account will be deleted by the end of the week to make space for new users. If you want your account data to be saved and sent over, please fill in the following details: First name Last name Email ID Password DOB Regards, |
In Cybersecurity interview questions, this is widely asked by the interviewers. You may frame the answer this way.
This mail is a clear case of phishing.
This will require a proper execution of different practices and support from the team. The practices include -
Additionally, I will take help from my team to monitor the attack's progress. This way, we can also use a DDoS protection service and scale up server capacity.
While there are multiple methods for detecting brute-force login attempts, I will use a Python script. It is one of the best and direct methods.
import re from collections import defaultdict from datetime import datetime, timedelta # Configuration LOG_FILE = "/var/log/auth.log" # Adjust for your system (e.g., /var/log/secure for CentOS) FAILED_PATTERN = r"Failed password for .* from (\d+\.\d+\.\d+\.\d+)" TIME_PATTERN = r"^([A-Za-z]{3} \d+ \d+:\d+:\d+)" THRESHOLD = 5 # Number of failed attempts TIME_WINDOW = timedelta(minutes=5) # Time window to check for brute-force # Helper function to parse log timestamp def parse_log_time(line): match = re.search(TIME_PATTERN, line) if not match: return None timestamp_str = match.group(1) current_year = datetime.now().year try: return datetime.strptime(f"{current_year} {timestamp_str}", "%Y %b %d %H:%M:%S") except ValueError: return None def detect_brute_force(): failed_logins = defaultdict(list) # {ip: [timestamps]} with open(LOG_FILE, "r") as file: for line in file: time = parse_log_time(line) if not time: continue match = re.search(FAILED_PATTERN, line) if match: ip = match.group(1) failed_logins[ip].append(time) # Check for brute-force attempts print("Possible brute-force attempts:") for ip, times in failed_logins.items(): times.sort() for i in range(len(times)): window = times[i:i + THRESHOLD] if len(window) == THRESHOLD and window[-1] - window[0] <= TIME_WINDOW: print(f"IP {ip} had {THRESHOLD} failed attempts between {window[0]} and {window[-1]}") break if __name__ == "__main__": detect_brute_force() |
I would use a Python script to create a MD5 hash of a file.
import hashlib def compute_md5(file_path): hash_md5 = hashlib.md5() try: with open(file_path, "rb") as f: for chunk in iter(lambda: f.read(4096), b""): hash_md5.update(chunk) return hash_md5.hexdigest() except FileNotFoundError: print(f"File not found: {file_path}") return None except Exception as e: print(f"Error reading file: {e}") return None if __name__ == "__main__": file_path = input("Enter the path to the file: ").strip() md5_hash = compute_md5(file_path) if md5_hash: print(f"MD5 hash of '{file_path}': {md5_hash}") |
First, I would isolate the affected system from the network to prevent the potential spread of malware. Then, I would gather information from the user regarding recent downloads, email attachments, or websites visited.
After that, I would perform the following actions:
Finally, I would monitor the system to ensure the threat has been completely removed.
This is considered a security incident and requires immediate action.
I would also educate the employee on identifying phishing attempts to reduce future risks.
I would treat this as a high-priority data exposure incident.
Proper documentation and post-incident analysis would also be necessary.
Multiple failed login attempts from different locations may indicate a credential-stuffing or brute-force attack.
I would continue monitoring for any successful login attempts and escalate the incident if necessary.
Ransomware incidents require rapid containment to minimize damage.
After recovery, I would perform a lessons-learned exercise and strengthen security awareness training across the organization.
There is no end to the number of cyber security interview questions one can go through before their interview. However, these should suffice for those who have completed their training and are certified. Become a part of the leading field of cybersecurity today and enjoy the ample opportunities that tag along.
You can start by researching the cybersecurity practices used by the company you are going to. Use some additional resources like articles or documents on cybersecurity interview questions.
The cybersecurity interview questions are basically a guide for candidates who want to build or improve their career in this field. It gives them enough information to excel in an interview.
These cybersecurity interview questions are divided into different sections. Each of these sections are curated for specific candidates including beginners, experienced, engineers, network experts, etc.
Cybersecurity helps protect sensitive information, prevents data breaches and ensures business continuity.
Common roles include Security Analyst, Network Security Engineer, SOC Analyst and Cybersecurity Consultant.
Explore Our Trending Articles -
Course Schedule
| Course Name | Batch Type | Details |
| Cyber Security Training | Every Weekday | View Details |
| Cyber Security Training | Every Weekend | View Details |